Google has enhanced its Kubernetes Engine (GKE) service with a few upgrades. Customers can now use GKE at scale, manage clusters with a web-based dashboard Cloud Console besides the supported kubectl command line interface, and harden the security by applying Google’s best practices for running a Kubernetes cluster.
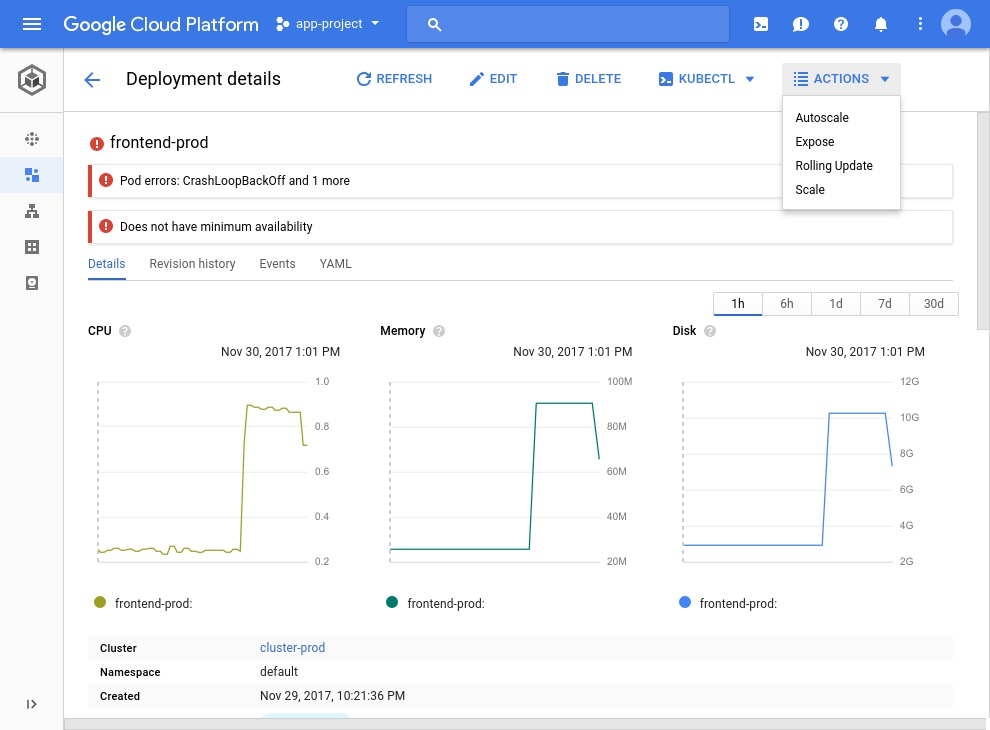
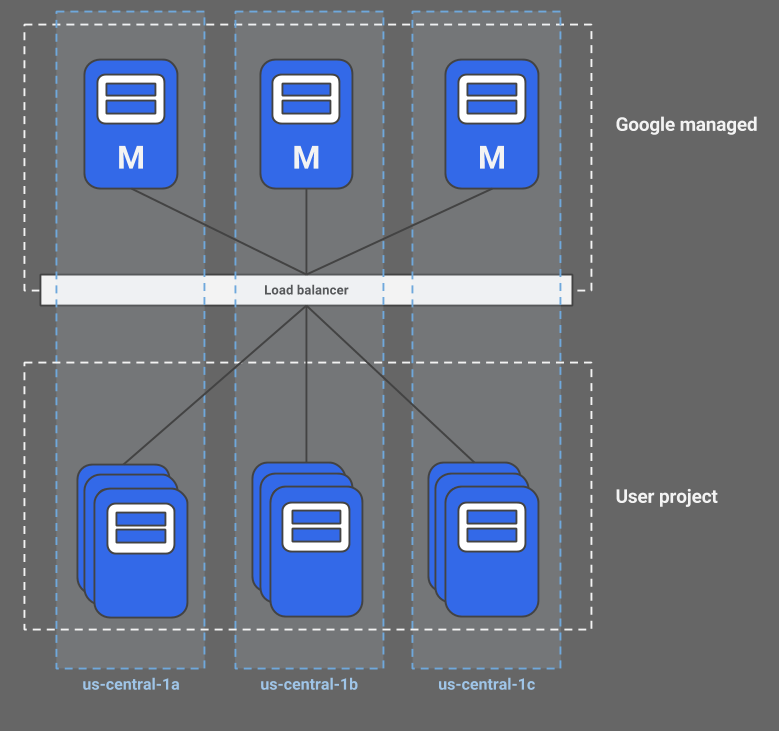
At the beginning of December, Google announced that the regional clusters in GKE are in beta and more scalable, which means customers can now create a Kubernetes cluster with multi-masters and a highly available control plane. The benefits of regional clusters are minimal downtime when upgrading masters and resilience of single zone failure. With the new Cloud Console for GKE customers can better manage clusters, troubleshoot, and perform any fixes. Moreover, Google provides several best practices regarding running a Kubernetes cluster. They recommend using the least privileged accounts for nodes, administrators to disable the Kubernetes Web UI (aka Kubernetes Dashboard) and legacy authorization in production environments.
With a Kubernetes regional cluster, the masters and nodes are spread across three zones, each by default having three nodes. The spread of master and nodes across zones ensures availability when one zone fails. Moreover, the availability and scalability can be further enhanced by increasing the number of nodes in each zone through the --num-nodes flag. More details about the regional cluster feature can be found in the documentation.
During the beta period of regional cluster feature of GKE, there will be no charges until GA. Finally, while setting up a cluster, Google recommends:
- Creating service accounts in the IAM section of the Cloud Console with the principle of least privileged before associating them to the nodes.
- Disable the Kubernetes Web UI when the cluster is up and running as it is backed by a highly privileged account.
- Disable the legacy authorization, that is the Attribute-Based Access Control (ABAC). In version 1.8 of Kubernetes, ABAC is disabled by default.
The security recommendation full details of running a Kubernetes cluster in GKE can be found on the Google Cloud Platform blog.
The three public cloud providers each now support Kubernetes through their services. Both Amazon and Microsoft have generic container orchestration tools available in their cloud platforms. However, both currently focus predominately on Kubernetes. Microsoft supports Kubernetes by a dedicated Azure Container Services for Kubernetes (AKS), which they rolled out last October and is in public preview. Amazon announced during their recent re:Invent that they would support Kubernetes through a new service named Amazon Elastic Container Service for Kubernetes (Amazon EKS), also in public preview.