Recently, Google announced the general availability (GA) of IAM Conditions and Tags for Cloud SQL, a fully-managed relational database service for MySQL, PostgreSQL, and SQL Server.
In August last year, Google first brought support for IAM Conditions for Cloud SQL, and Tags have been available since February of 2022, and both are now generally available. The company brings these features to improve Cloud SQL instances' management around access control. Akhil Jariwala, product manager at Google, wrote in a blog post on the generally available stated:
More Cloud SQL users mean more work ensuring that the right users have the appropriate access to the proper database instances. In the past, you may have addressed this challenge by separating Cloud SQL instances into distinct projects, isolating access along project boundaries. However, this approach can lead to a sprawling number of projects that can be burdensome to manage.
Also, separating instances by project does not work when access privileges vary within groups of instances that should stay in the same project, such as replication groups. Therefore, the features provide an answer for that.
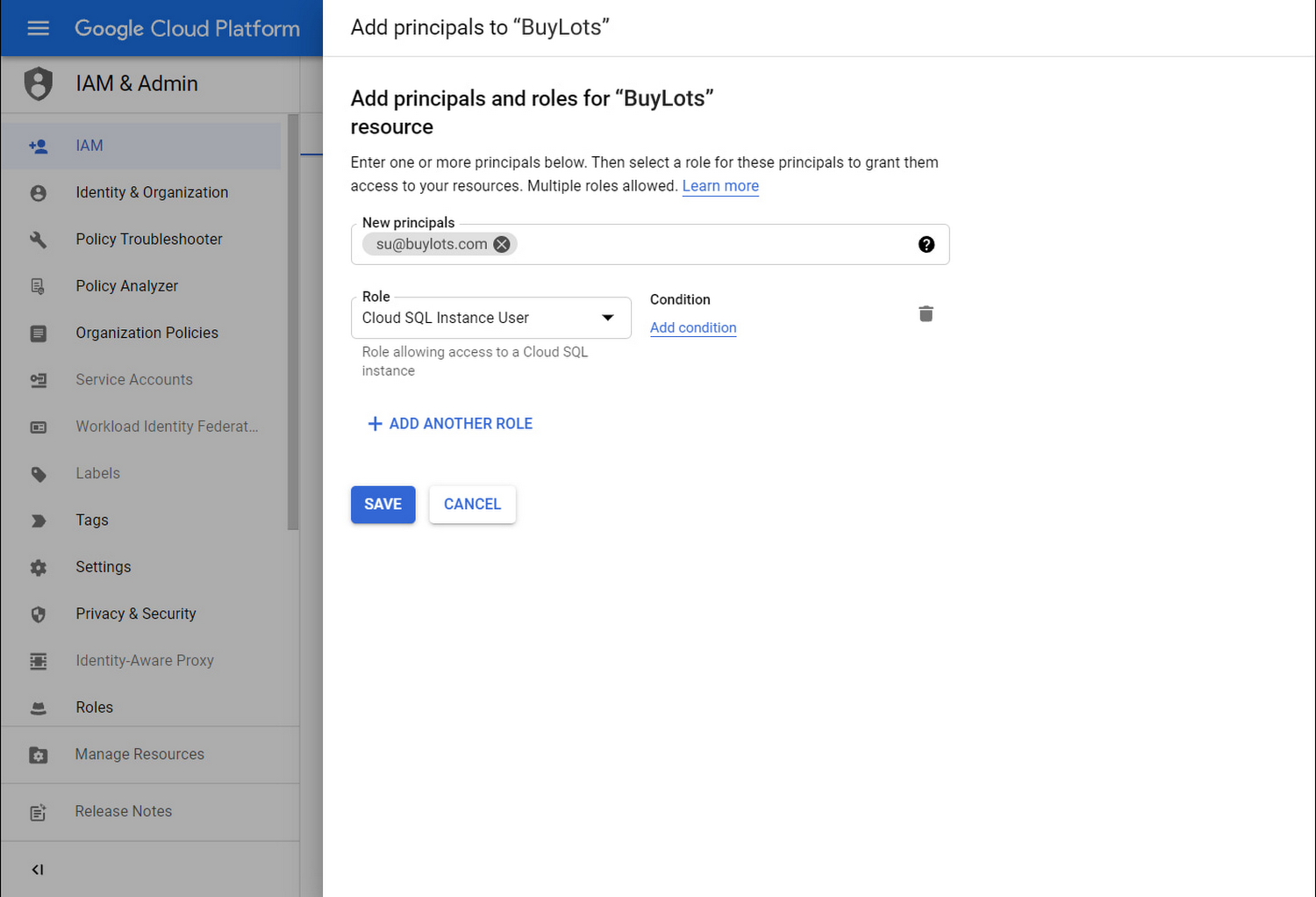
IAM Conditions are a part of Cloud Identity and Access Management (IAM), the service on which Cloud SQL and other Google Cloud services rely for access to cloud resources. Users of Cloud SQL can now add a condition as a property of an IAM policy binding, describing the circumstances in which a principal should have access to a Cloud SQL role.
Source: https://cloud.google.com/blog/products/databases/cloud-sql-launches-iam-conditions-and-tags
The IAM Conditions are welcomed, yet Hugo Hervieux, online developer at Ubisoft, tweeted:
Too few GCP services actually support IAM Conditions :/
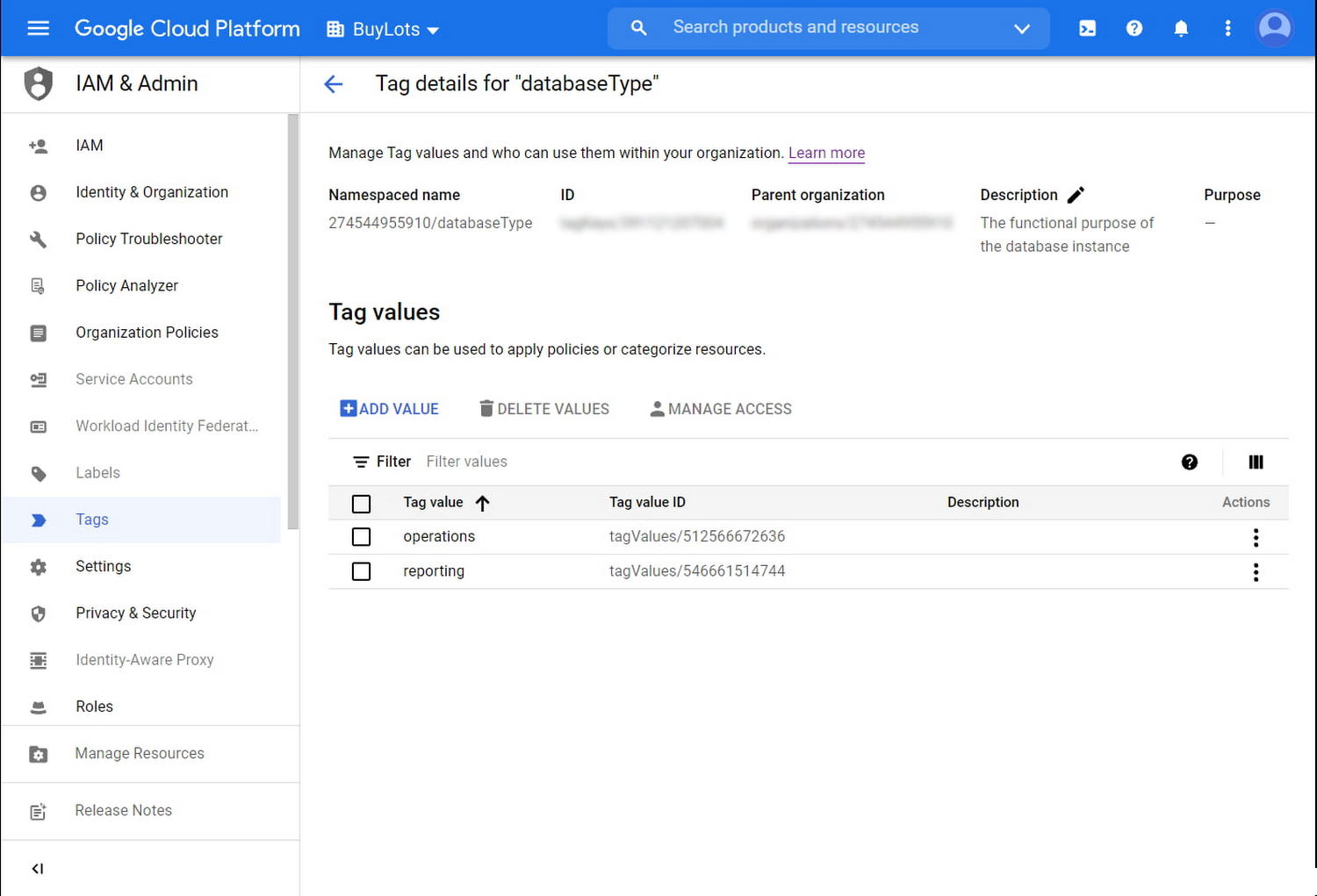
The other feature Tags are key-value pair resources that can be used to organize and govern access to other Google Cloud resources. Cloud SQL Users can manage Tags in Resource Manager and use Tags in IAM policy bindings to grant conditional access to resources that have those tag bindings. In addition, Cloud SQL instances can be assigned a tag or inherit one from the project or folder in which they are located.
A tag key could be a property-like environment, and a tag value could be an attribute like development or production. A tag can only have one value for a given key on a specific resource.
Source: https://cloud.google.com/blog/products/databases/cloud-sql-launches-iam-conditions-and-tags
Lastly, IAM Conditions and Tags can be used in conjunction to more securely and efficiently govern administrative and connection access to Cloud SQL. More details of IAM conditions and Tags are available on the respective IAM conditions documentation page and Tags documentation page.